Articles > Cybersecurity > How to prevent cyber security attacks
How to prevent cyber security attacks
This article was updated on October 10, 2024.

Written by J.L. Graff, MBA

Reviewed by Kathryn Uhles, MIS, MSP, Dean, College of Business and IT
Stats and facts behind cyber security attacks
In today’s digital world, staying vigilant is more important than ever. No one is immune to a cyber security attack; in fact, a cyber attack occurs every 39 seconds, with an average of 2,200 incidents daily. Many of these — nearly 86% — are financially motivated. Malicious actors work around the clock to gain unauthorized access to data, whether it’s to steal, damage or hold it for ransom. That means it’s essential to familiarize yourself with cyber threats and how to prevent them.
The key to avoiding a cyber attack is understanding systems and where vulnerabilities may exist. We have all heard that knowledge is power. That includes knowledge that focuses on defending networks, servers and data against unauthorized hacking attempts.
DIY ways to stay safe
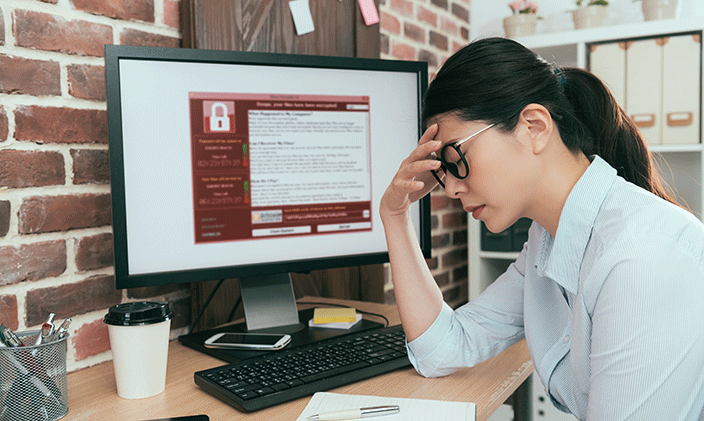
The following are some quick and easy steps you can take to safeguard your personal information from ransomware, malware, phishing attacks, hacking and other cyber threats.
Engage multifactor authentication (MFA)
Multifactor authentication is a layered security approach that allows you to use two or more authenticators to confirm your identity when logging in to your online accounts. This way, if one authenticator has been compromised, that second one is in place to safeguard your account.
Multifactor authenticators usually consist of something you know (e.g., password or PIN), something you have (e.g., smart card, mobile token or smartphone) and a biometric factor (e.g., voice recognition, facial recognition or fingerprint). As malicious hackers continue improving password-cracking techniques, MFA is more important than ever to protect your data.
Individuals can secure MFA by purchasing a security key, which is one of the most effective MFA methods on the market. Security keys can be inserted into your computer or used wirelessly; some even have built-in fingerprint biometrics.
If you don’t want to carry a security key or are worried about losing it, you can use an authentication application on your phone. When logging into an account, the authentication app will send you a one-time authenticator code to log in successfully. Popular MFA options include Google Authenticator and Microsoft Authenticator.
Watch out for social engineering attacks
Estimates identify 98% of cybercrime results from social engineering tactics. Hackers will use phishing (email), vishing (voice phishing) and SMiShing (SMS text messages) attacks to gain access to your data.
Have you received an email or text message that appeared to come from a legitimate source but had a weird email when you inspected the sender’s address? That is a phishing attack. A phishing attack is a social engineering tactic to deceive recipients into clicking a link, sending confidential information or downloading malware that gives hackers access to data.
Malicious hackers use tactics that appeal to fear, urgency, curiosity or greed. Once hackers have accessed your data, they can charge your credit cards, steal photos and videos, impersonate you, drain your bank account, compromise your network or withhold your information until you pay them a ransom.
Watch out for phishing attacks
Phishing has become alarmingly common in recent years. According to Cisco, 80% of the ransomware attacks it observed in 2022 began with a phishing email. And CompTIA reported a 48% rise in phishing attacks during the first half of 2022.
The following are some ways you can mitigate your vulnerability and reduce cyber attacks:
- Be creative with the naming convention of your email address. Uncommon email addresses will make it more difficult for hackers to send you phishing emails.
- Pay close attention to hyperlinks, content and the email domain. All are opportunities to identify red flags like grammatical errors, misspellings or the use of numbers rather than letters.
- If you are unfamiliar with the source of the email, voice message or text message, do not respond, open or click on anything.
- Be cautious of pop-up windows.
- Avoid sharing personal data over text messages or emails.
- Be skeptical of communication with emotional lures, like “I’m in jail and need Amazon gift cards.” No one posts bail with gift cards.
- Update your browser frequently. When you implement the latest features and security fixes, you’re better protected from known security issues and you get added protection from viruses, phishing, scams and other cyber threats.
Protect your password
Hackers will attempt to gain access to your personal and financial information using several techniques to attack your passwords. One of these is the brute-force attack, which is when a hacker systematically discovers your password using combinations of letters, numbers and symbols (e.g., %*#$@).
To safeguard your passwords from brute-force attacks, you should create passwords that are complex and long (a minimum of 12 characters recommended) and avoid using common words. A password combination of letters, numbers and special characters is ideal.
Another technique hackers use is the dictionary attack, where attackers try to steal your password using preselected lists of dictionary words, often beginning with commonly used words.
The solution? Avoid using common words in your passwords, and include upper and lowercase letters, numbers and special characters when permitted. Also, consider implementing the following:
- Avoid using the same password for multiple accounts.
- Stay away from using patterns or common passwords such as 123456, 654321, or 111111 for passwords. Similarly, eschew the use of adjacent characters, such as qwerty.
- Use a password manager to store your passwords securely. We often use passwords we will remember, but they may be easier for hackers to crack. Creating strong passwords that can be stored securely and that we do not have to remember is a more reliable solution.
- Change your passwords regularly, including your Wi-Fi password.
- Use biometric scans such as fingerprint or facial recognition when available.
- Do not use personal information such as your name, birthday or street name in your passwords.
- Avoid dictionary words.
Stay cyber savvy
While social engineering and brute-force hacks are common cyber attacks, they aren’t the only ones. Here are more ways you can prevent becoming a victim of cybercrime.
- Avoid or severely limit the personal information you share online. (Social media, anyone?)
- Make sure to establish the most secure privacy settings you’re comfortable with for your phone, email and browsers.
- Avoid or limit using location features.
- Keep your computer software up to date.
- Back up personal information regularly.
- Encrypt sensitive information.
- Use videos, literature, blogs, training, workshops, academic credentials and industry certifications to learn up-to-date cybersecurity measures.
- Trust your intuition. Remember, if something sounds too good to be true, it probably is.
Learn about cyber security attacks and more
Cyber security attacks are just the tip of the iceberg when it comes to what you'll learn when you study information technology and cybersecurity. Whether you are seeking a basic understanding, you’re a working professional looking to expand your IT skill set, or are interested in pursuing a career in the field, University of Phoenix offers online course collections, technology degrees and certificates to help you achieve your educational goals:
- Associate of Science in Cybersecurity
- Bachelor of Science in Information Technology
- Bachelor of Science in Cybersecurity
- Master of Science in Cybersecurity
- Certified Ethical Hacker Course Collection
- Certified Incident Handler Course Collection
- Computer Hacking Forensics Investigator Course Collection
- Advanced Cybersecurity Certificate
Request more information about these and other programs at University of Phoenix.
ABOUT THE AUTHOR
J.L. Graff is the Associate Dean in the College of Business and IT. He has served University of Phoenix since 2002 and has been a faculty member since 2008. He is a member of Epsilon Pi Tau and trustee for the UOPX Delta Sigma Chapter. He also served as a Scaled Agile Framework (SAFe®) Product Owner for three years where he worked on enhancing and improving the University’s business agility. He has served as a member of the board of examiners for Southwest Alliance for Excellence (SWAE) and the Future Data Reporting Group for the National Student Clearinghouse. He has served on committees for Pacific Association of Collegiate Registrars and Admissions Officers (PACRAO) and American Association of Collegiate Registrars and Admissions Officers (AACRAO). He is excited about the current and future state of information technology and helping students reach their academic and professional goals.

ABOUT THE REVIEWER
Currently Dean of the College of Business and Information Technology, Kathryn Uhles has served University of Phoenix in a variety of roles since 2006. Prior to joining University of Phoenix, Kathryn taught fifth grade to underprivileged youth in Phoenix.
This article has been vetted by University of Phoenix's editorial advisory committee.
Read more about our editorial process.

FREE IT Programs Guide
Learn how 100% of our IT degree and certificate programs align with career-relevant skills.
Thank you
Download your pdf guide now. Or access the link in our email.